Method 1: Using PowerShell to Find the Source of Account Lockouts
Both the PowerShell and the GUI tool need auditing turned before the domain controllers will log any useful information.
Step 1: Enabling Auditing
The event ID 4740 needs to be enabled so it gets locked anytime a user is locked out. This event ID will contain the source computer of the lockout.
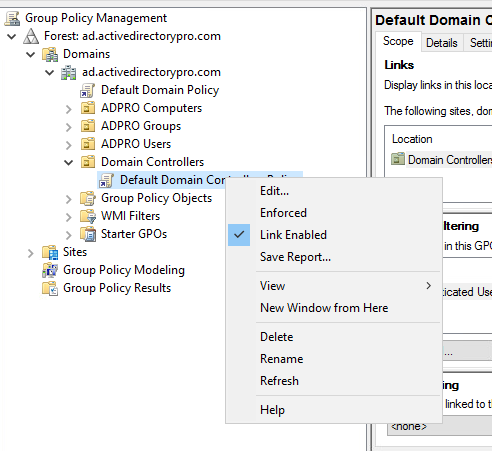
1. Open the Group Policy Management console. This can be from the domain controller or any computer that has the RSAT tools installed.

2. Modify the Default Domain Controllers Policy
Browse to the Default Domain Controllers Policy, right click and select edit.
3. Modify the Advanced Audit Policy Configuration
Browse to computer configuration -> Security Settings -> Advanced Audit Policy Configuration -> Audit Policies -> Account Management
Enable success and failure for the “Audit User Account Management” policy.
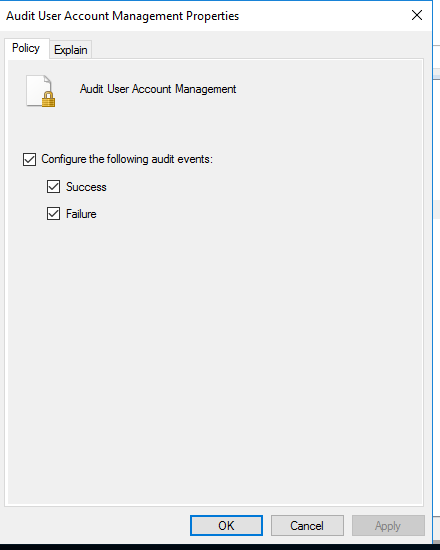
Auditing is now turned on and event 4740 will be logged in the security events logs when an account is locked out.
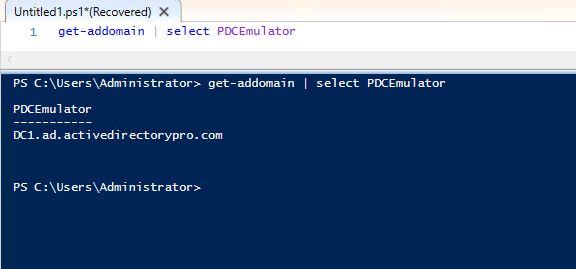
Step 2: Find the Domain Controller with the PDC Emulator Role
If you have a single domain controller (shame on you) then you can skip to the next step…hopefully you have at least two DCs.
The DC with the PDC emulator role will record every account lockout with an event ID of 4740.
To find the DC that has the PDCEmulator role run this PowerShell command
get-addomain | select PDCEmulator
Step 3: Finding event ID 4740 using PowerShell
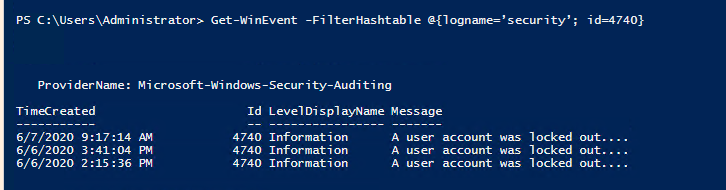
All of the details you need is in event 4740. Now that you know which DC holds the pdcemulator role you can filter the logs for this event.
On the DC holding the PDCEmulator role open PowerShell and run this command
Get-WinEvent -FilterHashtable @{logname=’security’; id=4740}This will search the security event logs for event ID 4740. If you have any account lockouts you should a list like below.
To display the details of these events and get the source of the lockout use this command.
Get-WinEvent -FilterHashtable @{logname=’security’; id=4740} | fl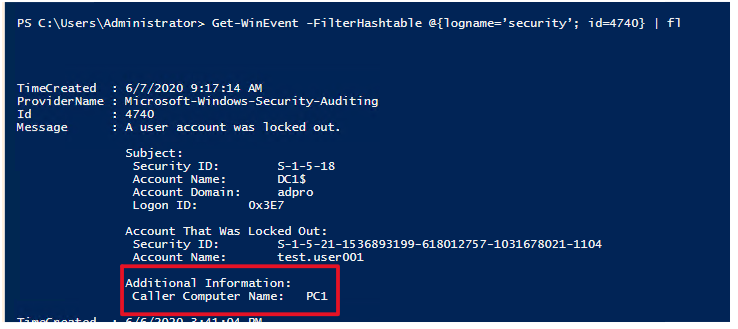
This will display the caller computer name of the lockout. This is the source of the user account lockout.
You can also open the event log and filter the events for 4740
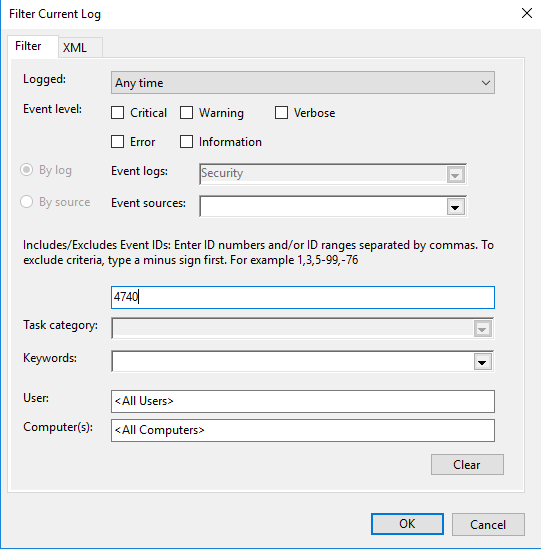
That is it for method 1.
Although this method works it takes a few manual steps and can be time consuming. You may also have staff that is not familiar with PowerShell and need to perform other functions like unlock or reset the users account.
That is why I created the Active Directory User Unlock GUI tool. This tool makes it super easy for staff to find all locked users and the source of account lockouts.
Check out the steps below for using the unlock gui tool.
Method 2: Using the User Unlock GUI Tool to Find the Source of Account Lockouts
I created this tool to make it super easy for any staff member to unlock accounts, reset passwords and find the source of account lockouts.
Just like PowerShell this tool requires the auditing be turned on for Account Management. See steps above for enabling these audit logs.
1. Open the User Unlock Tool
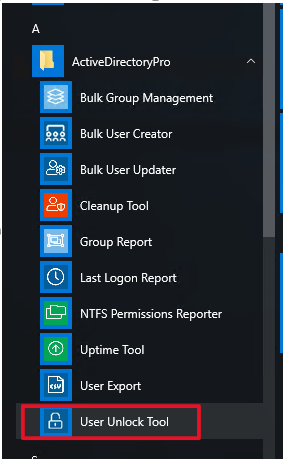
2. Click the Search Button, then click more details
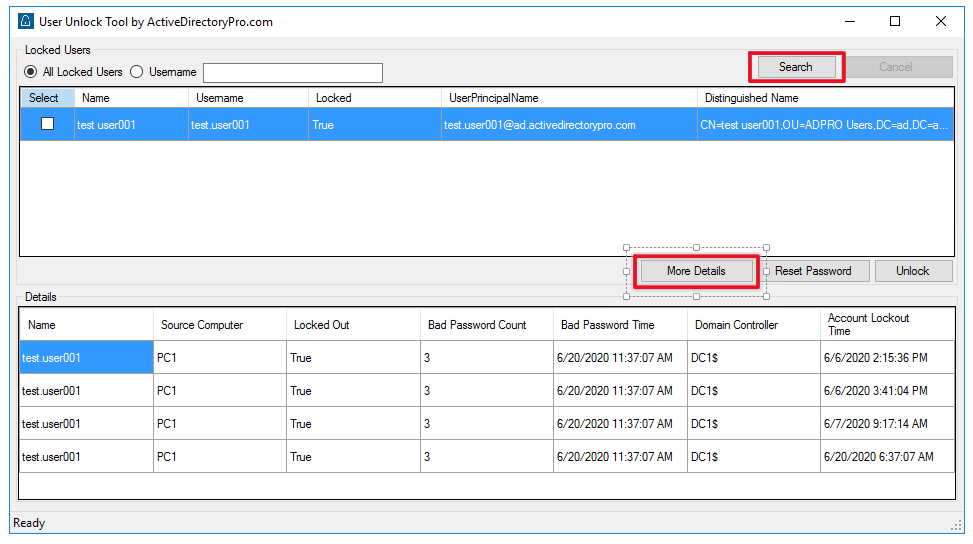
That is all there is to it.
You will now see a list of times the account was locked out and the source computer.
In addition you can unlock the account and reset the password all from one tool. The tool will display all locked accounts, you can select a single account or multiple accounts to unlock.
The user unlock tool is included in my AD Pro Toolkit bundle, this is a bundle of 10 tools to help simplify and automate routine AD tasks.

0 Comments